Which is true about testing a method with three integer parameters and one integer return value? O a. A good programmer would test all possible input values O b. Using a variety of calls involving assert() is a good way to test the method O c. Three test vectors are likely sufficient O d. Each test case should include a negative value as a parameter Which method name is valid? O a. calcAverage() O b. calc Average() c._calcAvg() O O d. calc_average()
Answers
The statements that are true are;
b. Using a variety of calls involving assert() is a good way to test the method
The method name that is valid is d. calc_average()
How to determine the statementTesting a method with three integer parameters and one integer return value involves using a variety of calls involving assert() is a good way to test the method.
Also, Option D "calc_average()" is a recognized method name in most programming languages when it comes to the method name.
The method name adheres to tradition by separating words with underscores and lowercase letters.
The method names in Options A and B contain spaces, which are normally forbidden in programming. Option C, which begins with an underscore and might be appropriate in some circumstances, is less popular and is not often advised.
Learn more about integers at: https://brainly.com/question/929808
#SPJ4
Related Questions
Write a single statement that prints outsideTemperature with a + or – sign. End with newline. Sample output:
+103.500000
#include
int main(void) {
double outsideTemperature = 103.5;
printf("%+lf\n", outsideTemperature);
return 0;
}
Answers
The following single statement can be used to print the value of the variable outsideTemperature with a + or - sign:
printf("%+lf\n", outsideTemperature);
This statement uses the format specifier %+lf to print the value of the double variable outsideTemperature with a sign (+ or -) and a precision of six decimal places (%lf), followed by a newline character (\n) to move to the next line.
To print the outsideTemperature with a '+' or '-' sign and end with a newline, use the following statement:
c : printf("%+lf\n", outsideTemperature);
Here's a breakdown of how it works:
1. printf() is a function used for printing formatted output.
2. "%+lf\n" is the format specifier where:
- % is the starting point of a format specifier.
- + indicates that a sign (+ or -) should always be displayed for the number.
- l specifies that the variable is a double.
- f is used for printing floating-point numbers.
- \n is an escape sequence that represents a newline character.
3. outsideTemperature is the variable being printed with the specified format.
Using printf("%+lf\n", outsideTemperature);, you can successfully print the `outsideTemperature` with a '+' or '-' sign, followed by a newline.
To know more about format specifier visit:
https://brainly.com/question/29354724
#SPJ11
Which of the following is a visual thinking tool that aids students in organizing ideas through analysis, synthesis, and comprehension?
mind map
outliner
outline
drawing
Answers
Answer:
mind map hope this help
Explanation:
The answer is:
mind mapthe ____ attribute can be used to identify where to download a plug-in.
Answers
The "src" attribute can be used to identify where to download a plug-in. In HTML, the "src" attribute is used to specify the URL of an external resource, such as an image, audio file, or plug-in.
When used with a plug-in, the "src" attribute indicates the location where the browser should download the plug-in from. For example, would instruct the browser to download the myplugin.exe file from the example.com website.
The `codebase` attribute is an HTML attribute that specifies the URL of the directory containing the downloadable plug-in files. When a browser encounters an embedded object requiring a plug-in, it can use this attribute to locate and download the necessary plug-in. This attribute is mainly used with the `` element in HTML to embed external content such as multimedia or plug-ins within a web page. By providing the `codebase` attribute, you ensure that users have access to the required plug-in to display or interact with the embedded content.
To know more about audio file visit:
https://brainly.com/question/30054984
#SPJ11
Write a program that HARDCODE a word, and then writes out that word once per line but for each line replace the first character of the word with a space and remove the last character of the word. Continue until no characters are left. (You will have to be careful with words having an odd number of characters.)
NOTE: As always, you can use input instead of hardcode.
Enter a word -->ABARACADABARA
ABARACADABARA
BARACADABAR
ARACADABA
RACADAB
ACADA
CAD
A
Answers
The program that illustrates the information will be:
public class Main
{
public static void main(String[] args) {
String s="ABARACADABARA";
int l=s.length()-1;//get the length of test string
System.out.println(s);
StringBuilder str=new StringBuilder(s);//Use string builder to replace characters
for(int i=0;i<s.length()/2;i++){
str.setCharAt(i,' ');//set character to space
}
What is a computer program?A computer program is a set of instructions written in a programming language that a computer can execute.
Software contains computer programs as well as documentation and other intangible components. Source code refers to a computer program in its human-readable form.
Learn more about program on:
https://brainly.com/question/23275071
#SPJ1
Hurry answerrrrrrr pleaseee
Select the correct answer
Rick is teaching a photography workshop about design and color in an image. He shows the students a few images to teach them about
contrast. Which is the correct way to show color contrast?
A bright colors against bright surroundings
О В.
bright colors against dull surroundings
dull colors against dull surroundings
D.
dull colors against white-colored surroundings
Answers
Answer:
bright colors against dull surroundings im pretty sure
Explanation:
Answer:c
Explanation:
a user reports that her pc displays unwanted and unexpected pop-ups each time she opens the browser. since she is currently at her desk and connected to the company network, she was wondering if someone could come down and troubleshoot her computer. you are assigned to resolve the problem. what is the first best practice that you should employ when responding to the user's problem?
Answers
The first best practice to employ when responding to the user's problem is to gather more information about the issue. This will help you understand the nature of the problem and determine the appropriate troubleshooting steps to take.
To gather information, you can ask the user specific questions such as:
1. What type of browser are you using?
2. Are the pop-ups related to specific websites or random?
3. When did the pop-ups start appearing?
4. Have you installed any new software or extensions recently?
5. Do you have an antivirus software installed on your computer?
By asking these questions, you can gather important details that will help you identify the root cause of the pop-up issue. Once you have gathered the necessary information, you can analyze it to determine the most appropriate course of action. This could involve running a malware scan, disabling suspicious browser extensions, or updating the browser to the latest version.
To know more about information visit:
https://brainly.com/question/33427978
#SPJ11
Please help quick!!
question: 15
true or false? you can strengthen the encryption of a caesar cipher by shifting the letters twice (using
two keys).
Answers
"You can strengthen the encryption of a caesar cipher by shifting the letters twice (using two keys). The statement true or false? The answer is true.
Wht is Caesar Cipher?The statement is true because to strengthen the encryption we can shift the letters by the method of Caesar Cipher. The Caesar cipher is a method that modifies some text using an encryption algorithm to improve the message's integrity, secrecy, or security. Shift ciphers include the Caesar Cipher. Modulo operators are used by Shift Ciphers to encrypt and decrypt communications. K, the key for the Shift Cipher, is an integer ranging from 0 to 25. The Caesar cipher is named for Julius Caesar, who, according to Suetonius, employed it with a three-shift (A becoming D while encrypting, and D becoming A when decrypting) to safeguard military-related communications.
Learn more about Caesar Cipher: https://brainly.com/question/14298787
#SPJ4
what is the best way to create an image of my mac computer so i can reload my setup and data in case of a computer crash
Answers
Steps :
1. Select File > New Image > Blank Image in the Disk Utility Mac programme.
2. Choose where to save the disc image after entering a filename and, if necessary, tags.When you save the disc image file before opening it in the Finder, this is the name that
shows.
3. Enter the name of the disc image in the Name area.
4. Enter a size for the disc image in the Size area.
5. Select the disc format by selecting the Format pop-up menu after clicking.
6. Select an encryption option from the Encryption pop-up menu to encrypt the disc image.
7. After selecting a partition layout from the Partitions pop-up menu, click.
8. Select an option by clicking the Image Format pop-up menu.
9. Click Save, then click Done. Wherever you saved the disc image file in the Finder, Disk Utility generates the file and mounts its disc icon on your desktop and in the Finder sidebar.
10. Files should be copied to the mounted disc image in the Finder before being ejected.
11. Restore the disk image to a disk.
What is an backup image ?
Image backups are precisely what they sound like: an image of your entire operating system, complete with all of its files, executable programmes, and OS configurations.
Hence, backup image can be created according to above steps in case of a computer crash to save data.
You can learn more about backup image for finding information from the given link:
https://brainly.com/question/28300995
#SPJ4
In which place does essential computing of computer takes place at?
option
1]microprocessor
2]ram
3]motherboard
4]none
Answers
Answer:
123456789-0\(\lim_{n \to \infty} a_n fffff\)
Explanation:
Sort the options for formatting a table under the tab where they are located.

Answers
Answer:
yes those are the correct order
Explanation: post protected
Forests are crucial to the health of our planet because they __________. A. Can easily be cut down to make room for agriculture and cattle grazing B. Provide homes for species of plants that are used to make medicines C. Clean and protect the atmosphere by absorbing carbon dioxide and releasing oxygen D. Provide fuel and lumber for houses and industries
Answers
Answer:
C
Explanation:
Trees release oxygen :)
Answer:
C. clean and protect the atmosphere by absorbing carbon dioxide and releasing oxygen
Explanation:
Help fast pls
1896
1950
1966
2006

Answers
The option that describes the computer buying experience is D. Computer hardware and software were sold together in bundles.
How to explain the informationThe computer purchasing experience can be best typified as the sale of associated hardware and software together in convergence.
In the primitive stages of private computing, this was immensely encouraged as both operating systems and supplementary programmes were dispensed by the originators of the compelling device - procuring everything needed in a sole purchase.
Learn more about computer on
https://brainly.com/question/24540334
#SPJ1
d) Are all cultures equally afraid of spiders? Explain.
Answers
Many of cultures in these regions consider spiders to be a symbol of good luck or a culinary delicacy
After teaching a group of students about the indications for use for aminoglycosides, the instructor determines that the teaching was successful when the students identify which type of infection as a primary indication
Answers
It is also essential that you do not drink milk within two hours (either before or after) of carrying tetracycline. This is because both food and milk can reduce the amount of medicine absorbed by your body, making it less useful in fighting infection. The tablets can cause throat tingle
What are the 4 types of infections?
The four different classifications of infectious agents are bacteria, viruses, fungi, and parasites. When studying these agents, researchers separate them using certain characteristics: Size of the spreading agent
What is disease and its types?
Infection happens when germs enter your body and multiply, resulting in disease. The four main kinds of infections are viral, bacterial, fungal, and parasitic.
To learn more about Infection, refer
https://brainly.com/question/25258835
#SPJ4
Write either True or False. a) Software is touchable part of computer system. b) System software provides easy interaction between user and computer c) Every computer needs to have own operating system. d) A computer can only understand the program written in assembly language. SANJIWANI Computer Book 7
Answers
Answer:
A: False B: False C: True D: False
Explanation:
Помогите пожалуйста исправить код и ответить на вопрос задачи. Что покажет этот код? PYTHON s = ‘Hi! Mister Robert' i = 0 while (i < (len(s))) and (count==0): if s[i] == ‘?': count+=1 i+=1 if count > 0: print("Найдено") else: print ("Готово")
Answers
Answer:
It checks if "?" exists in the string s. print Найдено if found, otherwise prints Готово
Explanation:
s = ‘Hi! Mister Robert'
i = 0
while (i < (len(s))) and (count==0):
if s[i] == ‘?':
count+=1
i+=1
if count > 0:
print("Найдено")
else:
print ("Готово")
Which of the following statements best explains how multitasking works in the human mind?
Answers
Answer: He's right
Explanation: I got the answer too
Recommend a minimum of 3 relevant tips for people using computers at home, work or school or on their SmartPhone. (or manufacturing related tools)
Answers
The three relevant tips for individuals using computers at home, work, school, or on their smartphones are ensure regular data backup, practice strong cybersecurity habits, and maintain good ergonomics.
1)Ensure Regular Data Backup: It is crucial to regularly back up important data to prevent loss in case of hardware failure, accidental deletion, or malware attacks.
Utilize external hard drives, cloud storage solutions, or backup software to create redundant copies of essential files.
Automated backup systems can simplify this process and provide peace of mind.
2)Practice Strong Cybersecurity Habits: Protecting personal information and devices from cyber threats is essential.
Use strong, unique passwords for each online account, enable two-factor authentication when available, and regularly update software and operating systems to patch security vulnerabilities.
Be cautious while clicking on email attachments, downloading files, or visiting suspicious websites.
Utilize reputable antivirus and anti-malware software to protect against potential threats.
3)Maintain Good Ergonomics: Spending extended periods in front of a computer or smartphone can strain the body.
Practice good ergonomics by ensuring proper posture, positioning the monitor at eye level, using an ergonomic keyboard and mouse, and taking regular breaks to stretch and rest your eyes.
Adjust chair height, desk setup, and screen brightness to reduce the risk of musculoskeletal problems and eye strain.
For more questions on computers
https://brainly.com/question/24540334
#SPJ8
suppose that logical and physical addresses in a paging system are 32-bits and that pages are 1k bytes with each frame number also being a 32-bit integer. what is the maximum size in bytes of the page table for each process
Answers
The maximum size in bytes of the page table for each process is 8MB multiplied by the size of the page table entry.
In a paging system, the page table is a data structure that maps logical addresses to physical addresses. The size of the page table is determined by the number of pages in the system and the size of each page. In this case, we are given that the pages are 1k bytes and the logical and physical addresses are 32-bits.
To calculate the maximum size in bytes of the page table, we need to consider how many pages can be addressed using 32-bit addresses.
Since each page is 1k bytes, we can address \(2^{20}\) pages (since \(2^{10}\) = 1k).
This means that we need 20 bits to represent each page number in the page table.
Since each process has its own page table, the maximum size of the page table for each process can be calculated as follows:
Since the physical address is 32 bits, the page table entry size is at least 32 bits + additional bits
The number of entries in the page table = number of pages in the system (\(2^{20}\))
Therefore, the maximum size of the page table for each process is \(2^{20}\) * (32 bits + additional bits) / 8 = 8MB * (32 bits + additional bits).
The additional bits may be used for flags or other information, such as permission bits for read, write, and execute access. The actual size of the page table may be smaller than this maximum size if not all pages in the system are being used by the process.
know more about data structure here:
https://brainly.com/question/24268720
#SPJ11
Helppppp meeeeee eee
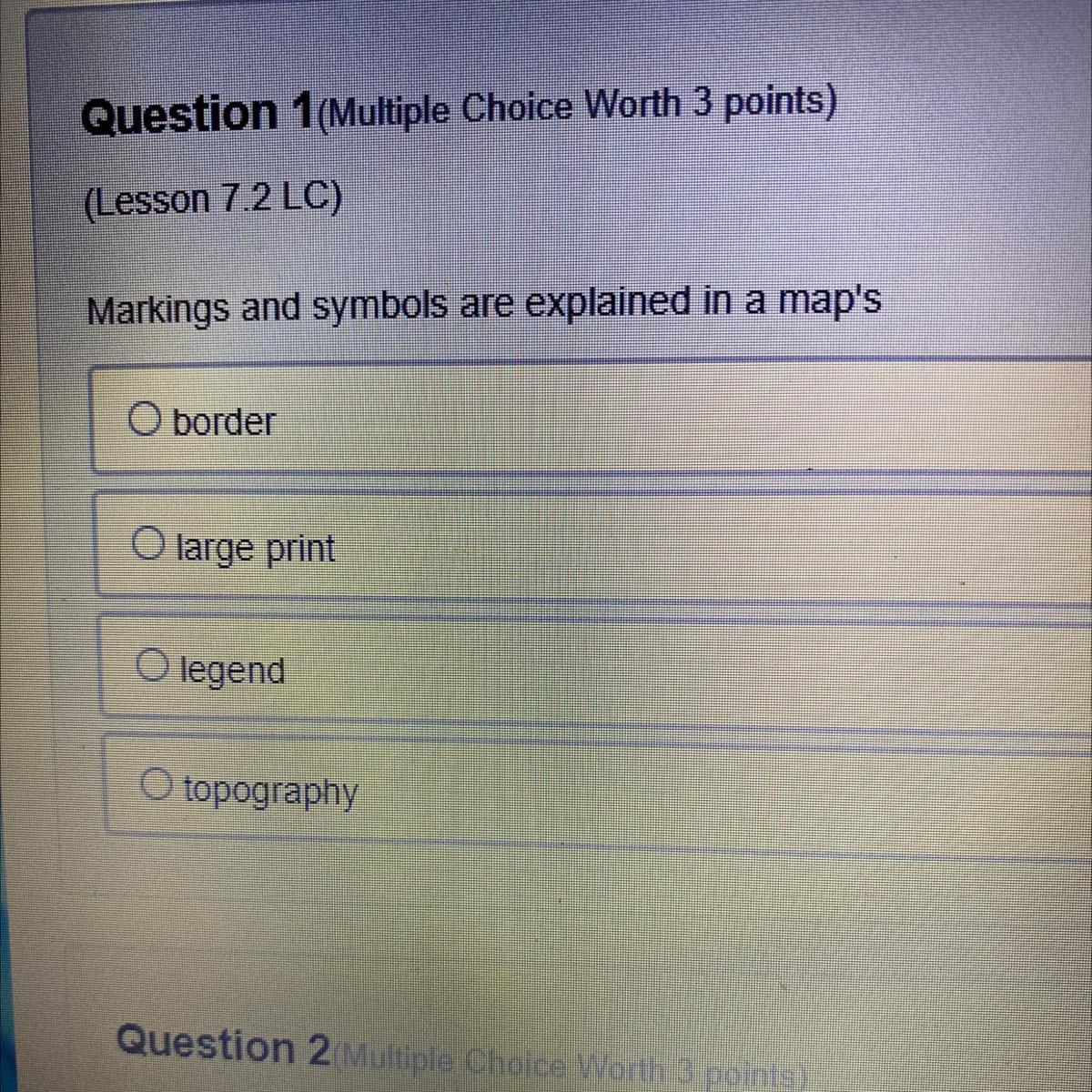
Answers
Answer:
Option C is correct
Explanation:
A map legend or key is a visual explanation of the symbols used on the map. It typically includes a sample of each symbol (point, line, or area), and a short description of what the symbol means.
How does the brain influence your emotions, thoughts, and values?
Answers
Amygdala. Each hemisphere of the brain has an amygdala, a small, almond-shaped structure. The amygdalae, which are a part of the limbic system, control emotion and memory and are linked to the brain's reward system, stress, and the "fight or flight" reaction when someone senses a threat.
What are the effects of the brain?Serotonin and dopamine, two neurotransmitters, are used as chemical messengers to carry messages throughout the network. When brain areas get these signals, we recognize things and circumstances, give them emotional values to direct our behavior, and make split-second risk/reward judgments.Amygdala. The amygdala is a small, almond-shaped structure found in each hemisphere of the brain. The limbic systems' amygdalae control emotion and memory and are linked to the brain's reward system, stress, and the "fight or flight" response when someone perceives a threat.Researchers have demonstrated that a variety of brain regions are involved in processing emotions using MRI cameras. Processing an emotion takes happen in a number of different locations.To learn more about Amygdala, refer to:
https://brainly.com/question/24171355
#SPJ1
MAP At a computer disk drive factory, inspectors randomly pick a product from production lines to detect a failure. If the production lines are normal, this failure rate q0=10 −3. However occasionally some problems occur in the lines, in which case the rate goes up to q1=10−1. Let Hi-denote the hypothesis that the failure rate is qi . Every morning, an inspector chooses drives at random from the previous day's production and tests them. If a failure occurs too soon, the company stops production and checks the critical part of the process. Production line problems occur about once every 4 days, so we will say P(H1 )=0.25=1−P(H0 ) 1. Based on N, the number of drives tested up to and including the first failure, design a MAP test that will use N to determine which hypothesis is true. 2. Calculate the probability of 'false alarm' (i.e. our MAP test computed in previous part concludes that the rate is q1 wrongly) and the probability of 'missed detection' (i.e. our MAP test fails on detect that the rate is q 1). 3. Based on this, calculate the probability of detection error Pe.
Answers
1. Based on N, the number of drives tested up to and including the first failure, design a MAP test that will use N to determine which hypothesis is true.Test 1: H0: q0 and H1: q1Let P(H0) be the prior probability of H0 which can be calculated as follows:P(H0) = 1 − P(H1) = 1 − 0.25 = 0.75Let P(H1) be the prior probability of H1 which can be calculated as follows:P(H1) = 0.25Let the likelihood function be L(N) = (1 − qN) for H0 and L(N) = (1 − q1N) for H1.According to MAP, if L(N)P(H0) > L(N)P(H1), then H0 is true; otherwise H1 is true.
Thus the decision rule is given as follows:If (1 − q0N) 0.75 > (1 − q1N) 0.25, then choose H0.Otherwise, choose H1.2. Calculate the probability of 'false alarm' (i.e. our MAP test computed in the previous part concludes that the rate is q1 wrongly) and the probability of 'missed detection' (i.e. our MAP test fails on detect that the rate is q1).False alarm:Probability of false alarm = P(H1) P(D|H1)/P(D)where P(D|H1) is the probability of getting the test results under H1.The probability of the drive not failing is 1 − q1.The probability of the drive failing on the Nth day is q1(1 − q1)N − 1Hence, P(D|H1) = q1(1 − q1)N − 1And, P(D) = P(D|H0)P(H0) + P(D|H1)P(H1)False alarm = 0.25 * q1(1 − q1)N−1/[(1 − q0N)0.75 + 0.25 * q1(1 − q1)N − 1]Probability of missed detection:Probability of missed detection = P(H1) P(-D|H1)/P(-D)where P(-D|H1) is the probability of getting the test results under H1 when it is not true.
The probability of the drive not failing is 1 − q1.The probability of the drive not failing on the Nth day is (1 − q1)N.The probability of getting missed detection is P(-D|H1) = (1 − q1)NAnd, P(-D) = P(-D|H0)P(H0) + P(-D|H1)P(H1)Probability of missed detection = 0.25 * (1 − q1)N/[(1 − q0N)0.75 + 0.25 * (1 − q1)N]3.
Based on this, calculate the probability of detection error Pe.The probability of detection error is the probability that the test will give an incorrect result when H1 is true and it is given as follows:Pe = P(H1) P(-D|H1) + P(H0) P(D|H0)Detection error = 0.25 * (1 − q1)N + 0.75 * q1(1 − q1)N − 1/[(1 − q0N)0.75 + 0.25 * (1 − q1)N]
Learn more about probability of detection error Pe here,
https://brainly.com/question/31844563
#SPJ11
Use bubblesort to arrange the numbers 76, 51, 66, 38, 41 and 18 into ascending order. Write the list after each exchange of numbers. How many comparisons are there altogether?.
Answers
Below is the complete step wise solution of the arrangement given for the asked bubblesort.
Step-by-step explanation:
Bubble sort Original list is [76, 51, 66, 38, 41, 18] Iteration: 1
> Swap 76 and 51, since they are not in correct order. Now, the list becomes [51, 76, 66, 38, 41, 18]
> Swap 76 and 66, since they are not in correct order. Now, the list becomes [51, 66, 76, 38, 41, 18]
> Swap 76 and 38, since they are not in correct order. Now, the list becomes [51, 66, 38, 76, 41, 18]
> Swap 76 and 41, since they are not in correct order. Now, the list becomes [51, 66, 38, 41, 76, 18]
> Swap 76 and 18, since they are not in correct order. Now, the list becomes [51, 66, 38, 41, 18, 76]
> 5 swaps happened in this iteration
> List after iteration 1 is [51, 66, 38, 41, 18, 76] Iteration: 2
> Swap 66 and 38, since they are not in correct order. Now, the list becomes [51, 38, 66, 41, 18, 76]
> Swap 66 and 41, since they are not in correct order. Now, the list becomes [51, 38, 41, 66, 18, 76]
> Swap 66 and 18, since they are not in correct order. Now, the list becomes [51, 38, 41, 18, 66, 76]
> 3 swaps happened in this iteration
> List after iteration 2 is [51, 38, 41, 18, 66, 76] Iteration: 3
> Swap 51 and 38, since they are not in correct order. Now, the list becomes [38, 51, 41, 18, 66, 76]
> Swap 51 and 41, since they are not in correct order. Now, the list becomes [38, 41, 51, 18, 66, 76]
> Swap 51 and 18, since they are not in correct order. Now, the list becomes [38, 41, 18, 51, 66, 76]
> 3 swaps happened in this iteration
> List after iteration 3 is [38, 41, 18, 51, 66, 76] Iteration: 4
> Swap 41 and 18, since they are not in correct order. Now, the list becomes [38, 18, 41, 51, 66, 76]
> 1 swaps happened in this iteration
> List after iteration 4 is [38, 18, 41, 51, 66, 76] Iteration: 5
> Swap 38 and 18, since they are not in correct order. Now, the list becomes [18, 38, 41, 51, 66, 76]
> 1 swaps happened in this iteration
> List after iteration 5 is [18, 38, 41, 51, 66, 76] Iteration: 6
> 0 swaps happened in this iteration
> List after iteration 6 is [18, 38, 41, 51, 66, 76] Sorted list is [18, 38, 41, 51, 66, 76] total number of comparisons made = 5+4+3+2+1 = 15
To learn more about Bubblesort, visit: https://brainly.com/question/29325734
#SPJ4
how to implement a password policy
Answers
The following steps are to be followed to implement a password policy:
1. ENFORCE PASSWORD HISTORY
2. SET MAXIMUM PASSWORD AGE
3. SET MINIMUM PASSWORD AGE
4. SET COMPLEXITY REQUIREMENTS
5. CREATE A PASSPHRASE
6. IMPLEMENT MULTI-FACTOR AUTHENTICATION
What is a password policy?
By encouraging users to adopt secure passwords and to use them appropriately, a password policy is a set of guidelines meant to improve computer security. A password policy is frequently included in an organization's formal rules and may be covered in security awareness training. A rule that a password must abide by is the rule of password strength. For instance, a minimum of five characters may be required under laws governing password strength.
To learn more about password policy, use the given link
https://brainly.com/question/28114889
#SPJ4
Who is responsible for applying CUI markings and dissemination instruction?
A. Authorized common access card (CAC) holder
B. Authorized NIPRnet (Non-classified Internet Protocol Router (IP) Network) system
C. Authorized system access administrator
D. Authorized holder of the information at the time of creation
Answers
Authorized holder of the information at the time of creation. is responsible for applying CUI markings and dissemination instruction
What is CUI?
A CUI (common user interface) is a user interface designed to provide a consistent way of interacting with a computer system, regardless of the underlying hardware or software technology. It is a graphical user interface (GUI) that provides a unified look and feel across all programs and devices, allowing users to easily access and use them. The CUI also simplifies the process of learning how to use a computer by providing a unified, intuitive way for users to interact with the system. The CUI can include windows, menus, buttons, icons, and other graphical elements that allow users to access and manipulate data.
To learn more about CUI
https://brainly.com/question/24847632
#SPJ1
3-46. Indicate the importance of APIs. What have been the advantages of DBS in creating a developer platform?
3-47. Explain what it means to think "outside of the box" in the context of DBS.
3-48. How well is DBS prepared for the future? Based on: API University. What are APIs and how do they work?
Answers
APIs or Application Programming Interfaces are crucial for businesses that want to interact with other businesses or software and allow developers to create new applications by integrating existing services and data.
DBS has found several advantages in creating a developer platform, which include the following:Advantages of DBS in creating a developer platform: Creating a developer platform has several advantages for DBS. Firstly, DBS has access to a range of developers who can create new applications using DBS's APIs.
This can create new revenue streams for the bank and give customers more options for banking services.Secondly, a developer platform can help the bank increase its brand recognition and visibility among potential customers.
To know more about Programming visit :
https://brainly.com/question/14368396
#SPJ11
What is a best practice while traveling with mobile computer devices?
Answers
Answer:
Maintain positive physical control of devices at all times (Do not leave in hotel safe). Turn off unused wireless communications (e.g., Bluetooth®1, NFC, Wi-Fi). Disable GPS and location services (unless required). Do not connect to open Wi-Fi networks.
Explanation:
The best practice while travelling with mobile computing devices is to maintain possession of your devices and other government-furnished equipment (GFE) at all times. Unused wireless technologies, such as Bluetooth®1, NFC, and Wi-Fi, should be turned off. Turn off location and GPS services (unless required). Avoid logging onto unsecured WiFi networks.
Define NFC.
Near Field Communication is referred to as NFC. It is a technology that enables wireless data transmission over brief radio wave distances. It is possible to share small payloads of data between an NFC tag and an Android-powered smartphone or between two Android-powered devices thanks to the NFC set of communication protocols, which permits communication between two electronic devices over a distance of 4 cm or less. Through a straightforward configuration, NFC enables a slow connection that can be utilized to launch more powerful wireless connections.
To learn more about NFC, use the given link
https://brainly.com/question/3942098
#SPJ4
In access, what are the different parts of a database application called?.
Answers
Answer:
An application part can be as simple as a single table, or it can include several database objects, including tables, forms, reports, and even relationships. In Access, you can open up the Application Parts gallery to view the built-in parts.
Explanation:
You have received a worksheet in which the first and last name of each employee is in one cell. Which feature will enable you to break out first and last names into two columns
Answers
A feature which will enable you to break out first and last names into two columns is: text to columns.
What is a worksheet?A worksheet is also referred to as a spreadsheet and it can be defined as a file (document) which comprises cells that are arranged in a tabulated format (rows and columns), so that they can be used for formatting, arranging, analyzing, storing, calculating and sorting data on computer systems.
In Computer technology, text to columns is a feature of spreadsheet applications which will enable users to break out first and last names into two columns rather than having both the first and last name in one cell.
Read more on spreadsheets here: https://brainly.com/question/4965119
1.What is the output of the following program? [10 Marks]namespace ConsoleApp1{class Program{static void Main(string[] args){int i, j;int [,] A = new int[5,5];for (i = 0; i < 5; ++i){for (j = 0; j < 4; ++j){A[i,j] = i*j;}}for (i = 0; i < 5; ++i){for (j = 0; j < 4; ++j){if (i < 5){A[j, i] = A[i, j];}elsebreak;Console.Write(A[i, j] + " ");}Console.WriteLine();}Console.ReadLine();}}}
Answers
The program outputs the following rectangular array:
0 0 0 0
0 1 2 3
0 2 4 6
0 3 6 9
0 4 8 12
This is the correctly formatted C# program:
namespace ConsoleApp1{
class Program
{
static void Main(string[] args)
{
int i, j; // declare index variables used to iterate over the array A
int [,] A = new int[5,5]; // create a 5 by 5 array
/* Iterate over the array with the index variables i and j
and initialize each location A[i, j] with the product
of i and j. */
for (i = 0; i < 5; ++i)
{
for (j = 0; j < 4; ++j)
{
A[i, j] = i*j;
}
}
/* Iterate over the array again. This time, swap locations
A[i, j] with A[j, i] */
for (i = 0; i < 5; ++i)
{
for (j = 0; j < 4; ++j)
{
if (i < 5)
{
A[j, i] = A[i, j];
}
else
break;
// display the current location A[i, j]
Console.Write(A[i, j] + " ");
}
/* print a newline to prepare for the next line of printing
which corresponds to the next column i */
Console.WriteLine();
// pause and wait for user keypress before continuing
Console.ReadLine();
}
}
}
}
When executed, this program simply prints a rectangular array like so;
0 0 0 0
0 1 2 3
0 2 4 6
0 3 6 9
0 4 8 12
Learn more about predicting program output here: https://brainly.com/question/20259194